Every request tracked from intake to resolution
Resolve Buyer and Compliance Requests with a Provable Trail.
Route buyer follow-ups, advisory requests, and support work through one inbox with structured intake, owner assignment, SLA tracking, and a resolution trail reviewers can follow.
Share a queue of follow-ups or support work and we will show intake, ownership, SLA pressure, and resolution workflow under real conditions.
Best fit
Risk & AccountabilityExpand to Reviewer Operations when the workflow broadens.
Best for accountable security and compliance request operations with assignment, status flow, and communication history.
The Numbers Behind Structured Request Operations
0%
Faster Request Resolution
Structured intake, ownership routing, and status workflows cut resolution time compared to email-driven request management.
0%
Communication Trail Coverage
Every request carries its full communication history - assignment, status changes, and requester follow-up in one thread.
0x
Handoff Efficiency
Requests route to the right owner with context intact, eliminating repeated explanations across teams.
Risk & Accountability
Best for accountable security and compliance request operations with assignment, status flow, and communication history.
- Reviewer Operations: Add packs, questionnaires, and controlled reviewer handoff around the same request queue.
- ReadyOps: Add training, exercises, and emergency communications when the follow-up work includes readiness proof.
Need help choosing?
Compare bundles and module pricing to find the right starting point, then confirm fit in a walkthrough if your workflow is regulated or time-bound.
The Difference Between Scattered Requests And Structured Operations
Without Aurora
- Security and compliance requests arrive through email, Slack, and hallway conversations with no tracking
- Request ownership is unclear - items bounce between teams with no accountability trail
- Requesters follow up repeatedly because they cannot see status without asking someone
- Resolved requests vanish into closed tickets - no record of how or why they were resolved
- No way to report on request volume, resolution time, or team workload for planning
With Aurora
- Structured intake queue captures every request with metadata, priority, and automatic routing
- Every request assigned to a named owner with status lifecycle, handoff logging, and SLA tracking
- Self-service status visibility for requesters with structured updates and communication history
- Full resolution history with owner actions, evidence references, and closure justification preserved
- Operational analytics showing volume trends, resolution metrics, and workload distribution
From Intake To Defensible Resolution In Five Steps
01
Capture every request with category and priority
Log advisory, support, incident, and access requests with consistent intake fields from day one.
02
Route to the right owner in seconds
Notify owners and assignees immediately so triage starts from one accountable queue.
03
Coordinate in one thread
Keep requester-visible replies and private team notes together so handoffs do not lose context.
04
Track status with ownership at every transition
Move requests through lifecycle states with a named owner at each step.
05
Prove what was requested and delivered
Preserve assignment, status, and communication records for auditors, buyers, and internal reviews.
Key Capabilities
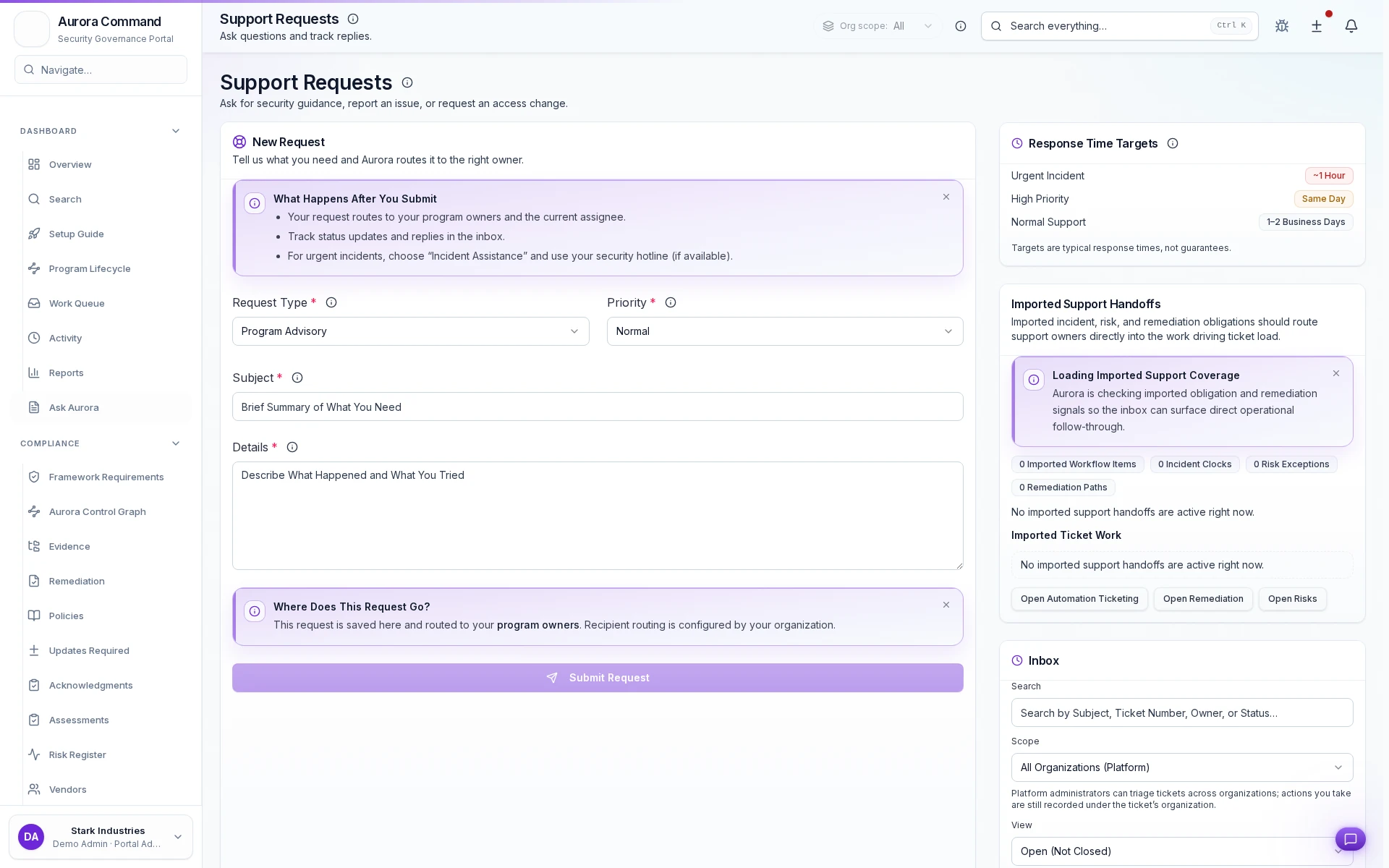
Standardized Intake, Zero Guesswork
Collect category, priority, and request details in one consistent format every time.
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Sync Requests With Your Existing Work Tools
Extend This Workflow
- GovernancePolicy lifecycle management, approval workflows, and control mapping for compliance programs.
- RiskRisk register, remediation ownership, and closure evidence across programs.
- Incident Readiness & ResponseVersioned runbooks, structured exercises, and remediation closure with evidence.
- Simulations & SessionsBroader tabletop scenarios and cross-team drills beyond incident-specific exercises.
Common Questions About Support Requests
Can our team handle both customer requests and internal follow-up in one place?
Can our team handle both customer requests and internal follow-up in one place?
Yes. Requester replies and private team notes are tracked separately in the same ticket record so teams can coordinate without losing external communication clarity.
Who can update status and assignment?
Who can update status and assignment?
Requesters and ticket managers can update status according to role permissions. Administrators can assign or reassign ownership as work moves between teams.
Can platform admins triage across organizations?
Can platform admins triage across organizations?
Yes. Platform administrators can use organization and platform inbox views while preserving per-ticket organization context and accountability.
Does this replace a full ITSM system?
Does this replace a full ITSM system?
This capability is built for security and compliance request operations: intake, assignment, status, and history. It complements broader ITSM tooling where needed.
Stop Losing Request Context Across Handoffs
Share your current ticket workflow and we will show how intake, handoffs, and closure become audit-ready.
Share one intake queue or follow-up workflow. We will show intake, assignment, status flow, and the full communication record.