People proof, not just policy proof
Turn Written Policies into Verified Employee Understanding.
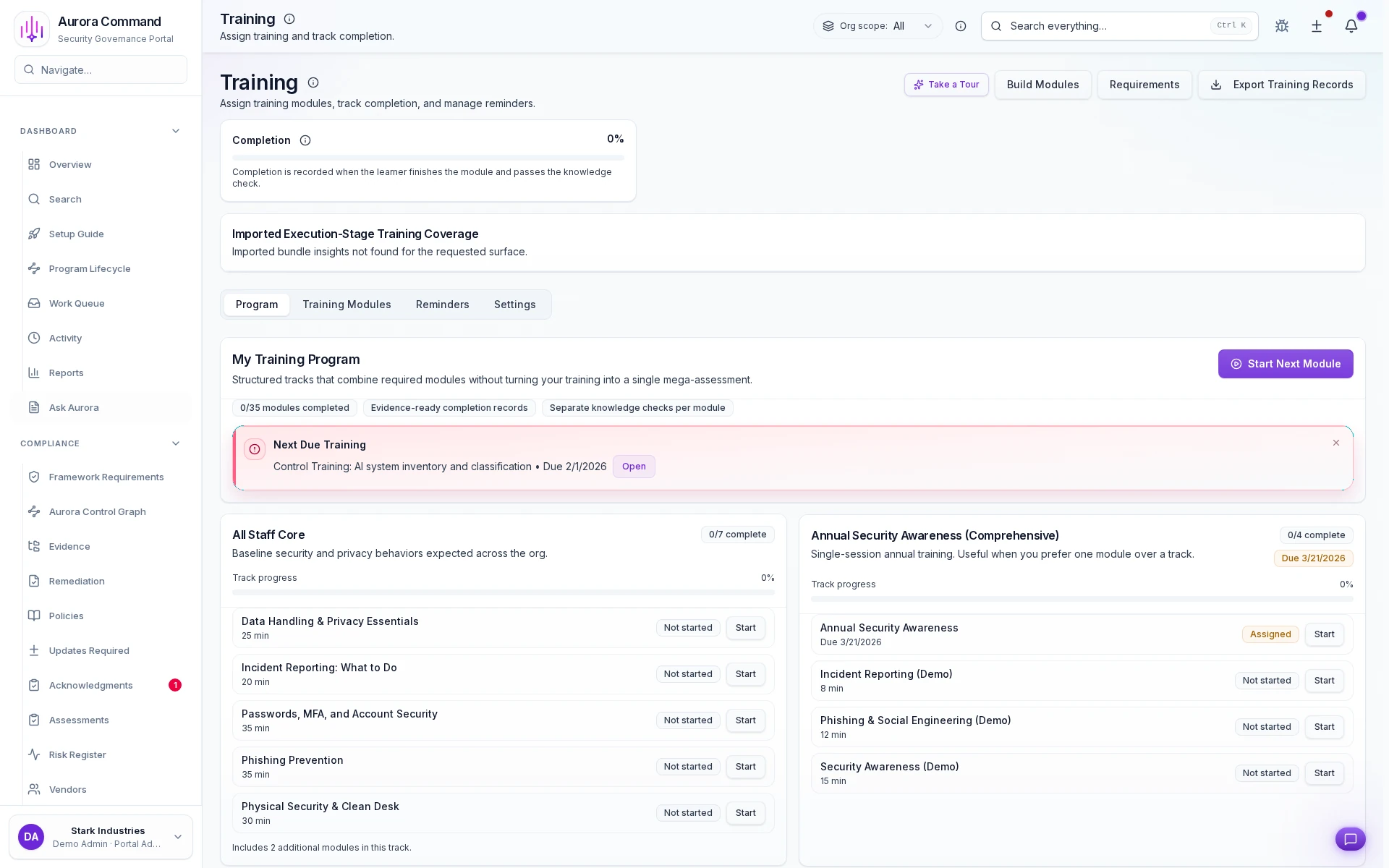
Assign training by role and cohort, track every completion in real time, collect signed attestations locked to the exact version each person reviewed, and export the evidence package auditors pull first, already mapped to the controls they will sample.
Pick a training control an auditor sampled last cycle. We will trace the assignment, completion, signed attestation, and control linkage end-to-end in under 15 minutes. No spreadsheet required.
Best fit
Workforce ReadinessExpand to Readiness Suite when the workflow broadens.
Best for training assignments and completion logs reviewers can sample.
Sample output
Training & attestation evidence package
Completion rates, signed acknowledgments, version-locked timestamps, and control mappings in one ready-for-review export.
SCIM-synced cohortsSigned attestationsControl-linked evidence
The Numbers Behind Verified Training Programs
0%
Completion Rate
Structured assignment workflows with deadline tracking and automatic reminders drive near-complete training coverage across cohorts.
0x
Attestation Depth
Training completions linked to specific policies and controls -- not just a checkbox, but proof of understanding mapped to requirements.
< 0 day
Assignment Turnaround
New hires and policy updates trigger automatic training assignments with role-based routing -- no manual spreadsheet management.
Workforce Readiness
Best for training assignments and completion logs reviewers can sample.
- Readiness Suite: Add exercises, incidents, and communications to connect training proof to broader operational readiness.
- Command: Add on-prem telemetry for regulated infrastructure.
Need help choosing?
Compare bundles and module pricing to find the right starting point, then confirm fit in a walkthrough if your workflow is regulated or time-bound.
The Difference Between Checkbox Training And Proven Understanding
Without Aurora
- Training tracked in spreadsheets that go stale -- nobody knows who completed what or when
- No connection between training and the policies or controls it's supposed to satisfy
- Attestation means clicking 'I agree' with no evidence of understanding or policy version
- New hire onboarding requires manually building a training checklist from scattered documents
- Auditor asks for training evidence and the team exports a vendor report with no control mapping
With Aurora
- Live completion dashboards with cohort breakdowns, deadline tracking, and automatic reminders
- Every training module linked to its governing policies and mapped to specific control requirements
- Structured attestation tied to specific policy versions with completion evidence and timestamps
- Role-based training paths auto-assigned at onboarding with progress tracking and escalation
- Training completions exported with policy linkage, attestation records, and control coverage mapping
From Written Policy To Demonstrated Understanding In Five Steps
01
Build SCIM-synced cohorts and assign training
Define cohorts by role, department, contractor status, or privilege level. Connected identity providers add new hires on day one and remove departures automatically so the roster always mirrors reality.
02
Track completions in real time
Live dashboards show who finished, who is in progress, and who is overdue. Filterable by cohort, due date, and risk tier. Slack and email nudges fire automatically so nothing slips past a review window.
03
Capture signed, version-locked attestations
Each attestation records the signer's identity, a cryptographic timestamp, and the exact policy or module version they reviewed. The result is a tamper-evident receipt proving the person engaged with the content, not just that it existed.
04
Map completions to framework controls
Every completion and attestation links to the specific controls that require awareness evidence: SOC 2, ISO 27001, HIPAA, or custom frameworks. Auditors can sample a control and land on the training proof instantly.
05
Export the full people-proof package
Generate a single PDF or CSV bundle containing completion rates, signed attestations, version history, and control mappings. Hand it to any auditor, buyer, or insurer with zero cleanup.
Key Capabilities
SCIM-synced, role-based assignment
Define cohorts by role, department, privilege level, or contractor status. SCIM integrations add new hires on day one and remove departures automatically so your training roster is always workforce-accurate.
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Your Training Roster Mirrors Your Workforce: Automatically
Extend This Workflow
- GovernancePolicy lifecycle management with version tracking and approval workflows.
- Simulations & SessionsBroader tabletop scenarios and cross-team drills beyond training exercises.
- Phishing ResiliencySimulated phishing campaigns with click-rate tracking and targeted retraining.
- Readiness LeaderboardGamified completion tracking with team rankings and recognition.
Questions Teams Ask About Training & Acknowledgments
Can we upload our own training content alongside built-in templates?
Can we upload our own training content alongside built-in templates?
Yes. Start with the included security-awareness and policy-acknowledgment templates, then upload custom modules, video, PDF, or interactive, for topics unique to your organization. Custom content inherits the same completion tracking, attestation collection, and control mapping as built-in material so auditors see one consistent evidence set.
How do training records connect to compliance controls?
How do training records connect to compliance controls?
Every training module maps to the specific controls that require awareness or acknowledgment evidence. When an auditor samples a control, say SOC 2 CC1.4 or ISO 27001 A.7.2.2, the completion record, attestation signature, and policy version are already linked. No manual cross-referencing or last-minute spreadsheet assembly.
How do SCIM-synced cohorts keep assignments current?
How do SCIM-synced cohorts keep assignments current?
Connect Okta, Entra ID, or Google Workspace via SCIM and cohorts update in real time. New hires inherit role-based assignments on day one, departures are removed automatically, and role changes trigger the correct re-assignment, so your training roster always mirrors your actual workforce without manual list management.
What exactly is captured in a signed attestation?
What exactly is captured in a signed attestation?
Each attestation records the employee's identity, a cryptographically timestamped signature, the exact policy or module version acknowledged, and the control requirement it satisfies. Auditors get a tamper-evident chain from the person who signed to the version they reviewed to the control that demanded it.
Can we set different due dates and recurrence schedules per cohort?
Can we set different due dates and recurrence schedules per cohort?
Yes. Assign unique deadlines and recurrence cadences by role, department, or custom cohort. Privileged-access teams can recur quarterly while general staff recurs annually. Overdue learners surface automatically in dashboards and via Slack or email reminders so nothing slips past a review window.
Stop Proving Policies Exist. Start Proving People Understood Them
Share one training control an auditor sampled. We will walk through the assignment, completion, signed attestation, and control linkage so you can see the full people-proof chain before you commit.
Share your training roster or control sample. We will show assignment, completion, and governed attestations.