Policies, approvals, and defensible history
Policies, Owners, and Approvals in One Governed Record
Policies, approvals, review schedules, training acknowledgments, and control ownership live in one governance record. When a reviewer asks what changed, who approved it, and when it was in force, the defensible answer is already there. No spreadsheet archaeology required.
Share one policy pack, review calendar, or control spreadsheet. We will show how approvals, owners, and framework mappings stay attached from first draft to final audit.
Best fit
Platform CoreExpand to Continuous Compliance when the workflow broadens.
Best for building the core program: controls, policies, approvals, and a reusable governance record.
Sample output
Governance approval trail
Versions & diffsApproval chainsMapped controls
The Difference Between Scattered Policies And Defensible Governance
Without Aurora
- Policies scattered across wikis, drives, and email threads with no ownership or approval trail
- Control frameworks maintained in spreadsheets that go stale weeks after the last review
- Approval workflows happen over email -- no record of who approved what or when
- Auditors ask for your control matrix and the team scrambles to build one from scratch
- Policy exceptions granted verbally with no documentation or expiry tracking
With Aurora
- Every policy version tracked with diff history, assigned owners, and timestamped approval signatures
- Controls linked to policies, evidence, and owners with automatic staleness alerts
- Structured approval chains with audit-ready timestamps and delegation records
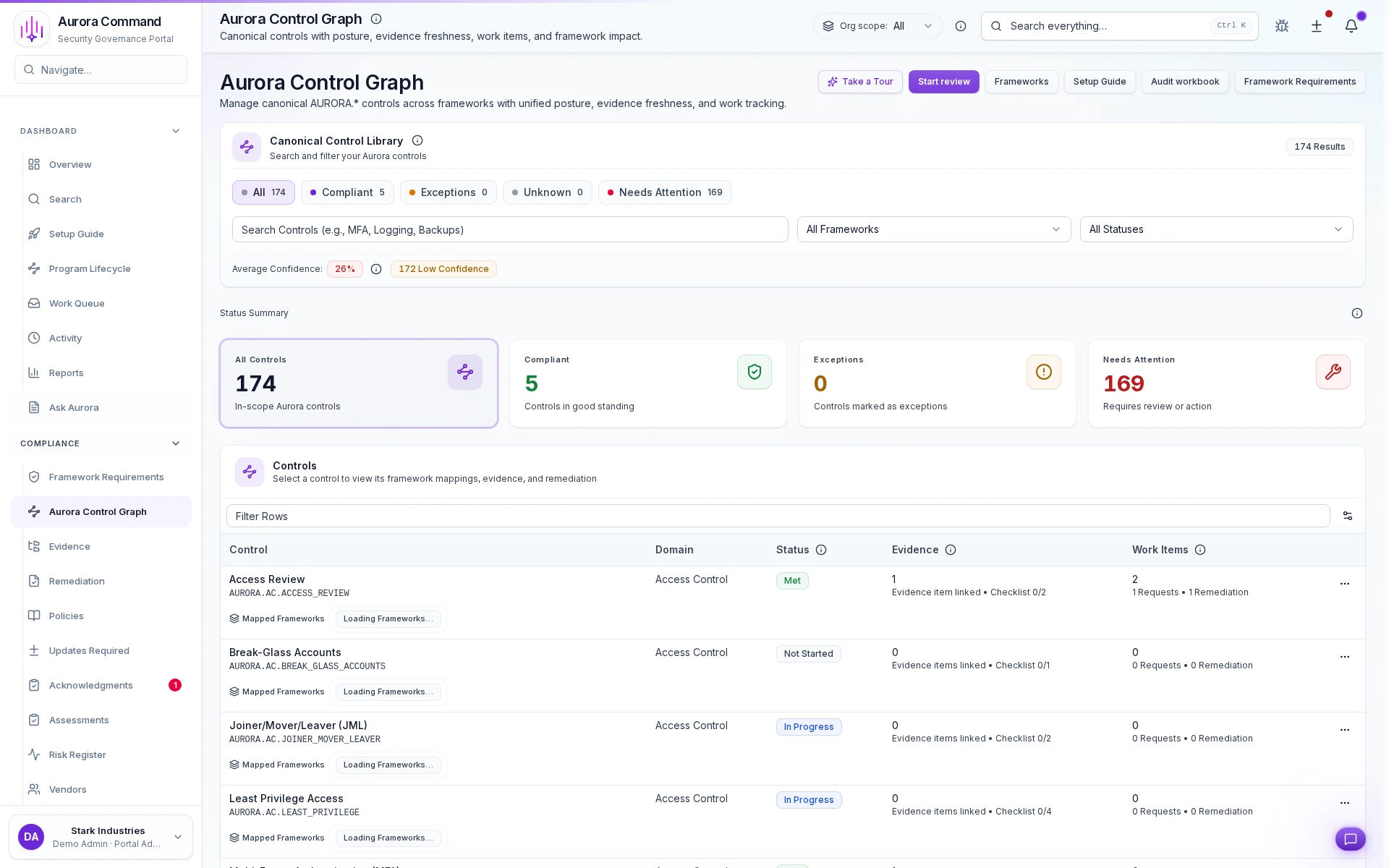
- Living control matrix with real-time coverage, linked evidence, and exportable snapshots
- Exceptions tracked with justification, approver, expiry date, and review reminders
Platform Core
Best for building the core program: controls, policies, approvals, and a reusable governance record.
- Continuous Compliance: Add integrations and scheduled checks so evidence stays current.
- Command: Add on-prem telemetry and unexpected-change monitoring for regulated environments.
Need help choosing?
Compare bundles and module pricing to find the right starting point, then confirm fit in a walkthrough if your workflow is regulated or time-bound.
The Numbers Behind Defensible Governance Programs
0%
Policy Coverage Improvement
Teams that assign every policy an owner and approval chain close coverage gaps faster than annual review cycles catch them.
0x
Faster Audit Preparation
Control matrices with linked evidence and approval history cut audit prep from weeks to days.
0%
Approval Trail Completeness
Every policy change, exception, and control update carries a timestamped approval signature reviewers can verify.
From First Draft To Defensible Governance Record
01
Import your existing policy library
Bring policies in any format. Ownership, review cadence, approval routing, and framework mapping attach on import, not blank-page rebuilds.
02
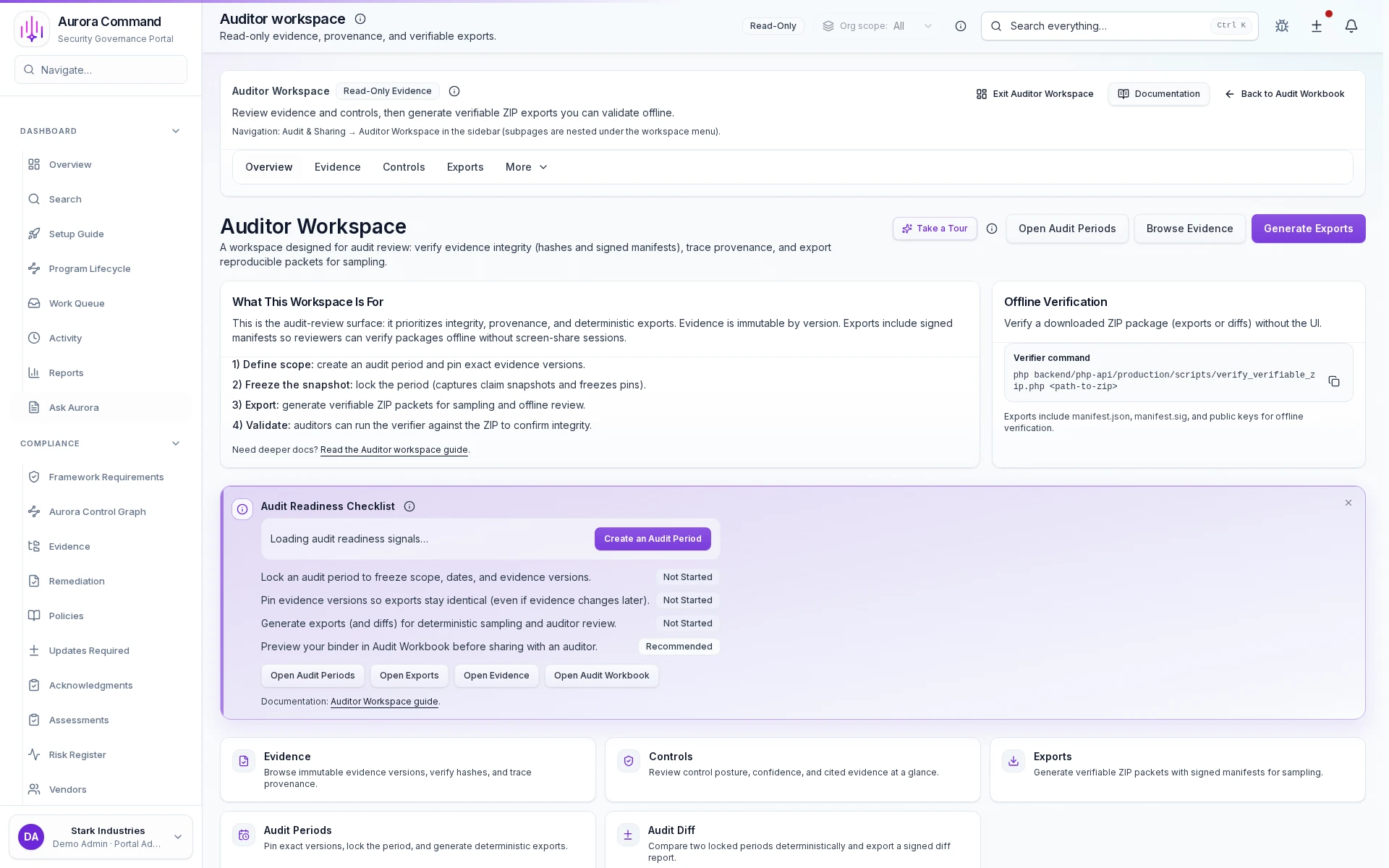
Log every approval with zero manual effort
Who reviewed it, what changed, when it was approved, and the exact diff. All captured automatically so the governance record writes itself.
03
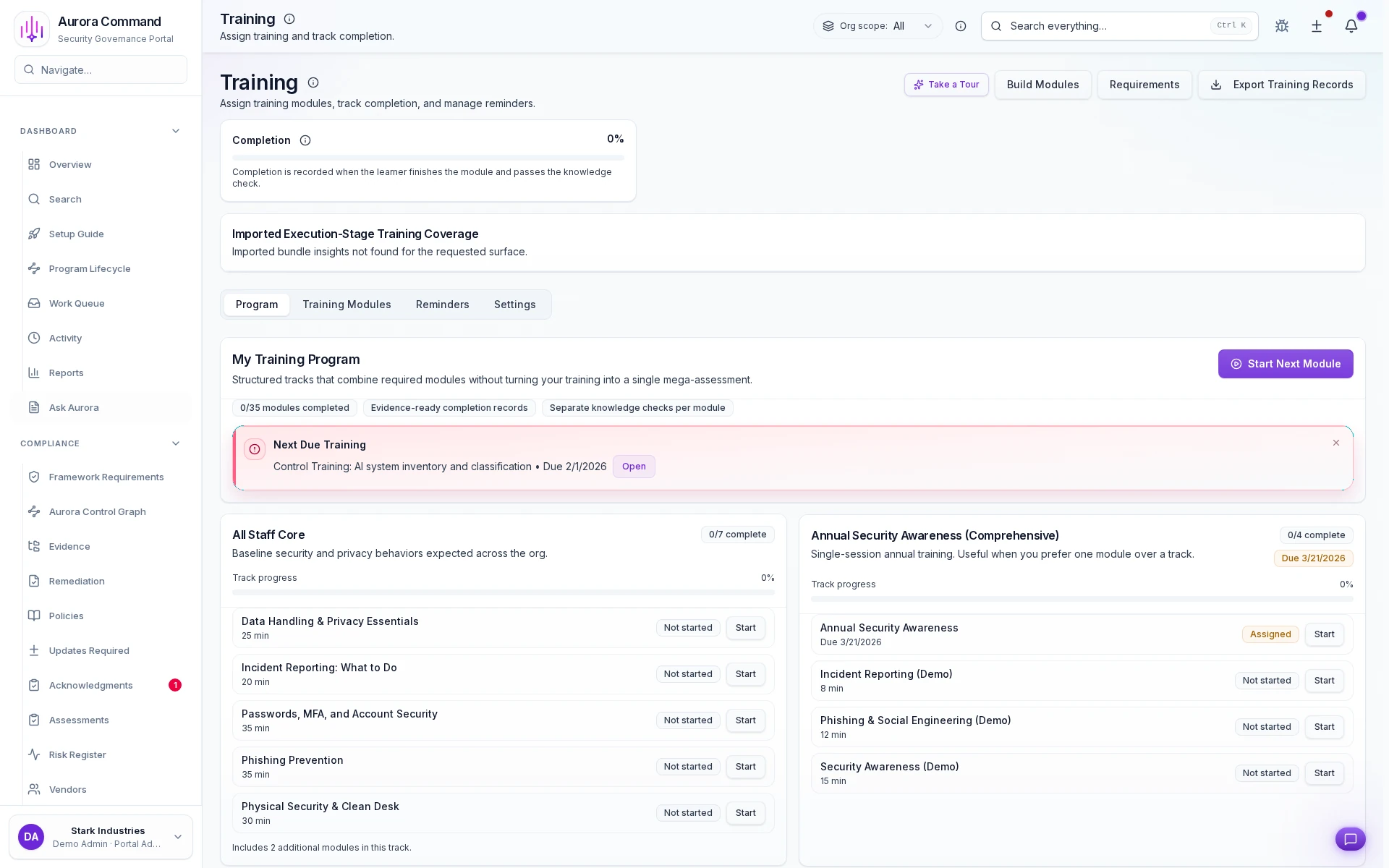
Link acknowledgments to the policies they cover
Training completions, signed attestations, and outstanding gaps stay bound to the policies and controls they satisfy, not in a separate tracker.
04
Preserve the defensible change trail across cycles
Version diffs, approval chains, and ownership transfers persist across review periods. Auditors sample any window without reconstruction.
05
Hand off evidence without exposing your workspace
Reviewers access policies, approvals, and full history through Trust Center tiers with time-bounded links. No workspace login required.
Key Capabilities
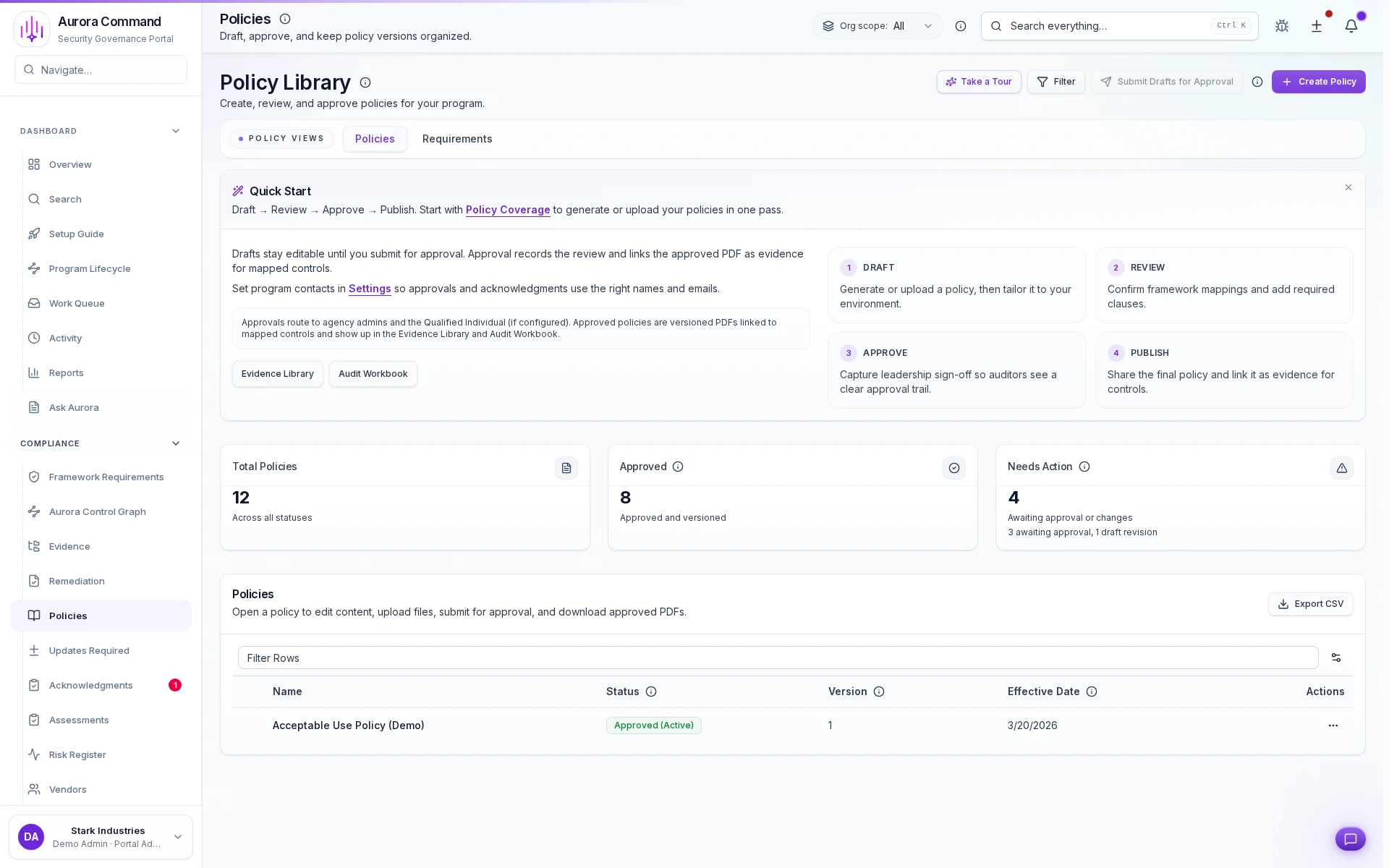
Versioned Policy Library
One library for drafts, approved versions, and publish state with inline diff views. No more chasing files across drives, inboxes, and shared folders.
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Pull Governance Context From The Tools Teams Already Use
Questions Teams Ask About Governance
Can we start with policies we already have?
Can we start with policies we already have?
Yes. Import existing policies in any format: Word, PDF, Google Docs, even spreadsheets. Aurora applies governance workflow on top: ownership, cadence, approval routing, and versioning. No starting from scratch.
How does versioning work?
How does versioning work?
Every policy change creates a new version with an inline diff view. Prior versions stay accessible for auditor comparison. Locked review periods preserve exactly what was in force during each audit window.
Can one control satisfy multiple frameworks?
Can one control satisfy multiple frameworks?
Yes. Map a single canonical control to overlapping requirements across SOC 2, ISO 27001, HIPAA, CMMC, and others. Evidence, owners, and approvals carry across frameworks without duplication.
What happens when a policy owner leaves?
What happens when a policy owner leaves?
Ownership transfers are logged as governance events with the transfer reason and approver. The new owner inherits the review schedule, pending approvals, and full history. The decision trail stays intact.
How do acknowledgments tie back to compliance controls?
How do acknowledgments tie back to compliance controls?
Signed attestations and training completions link directly to the policies and controls they satisfy. When an auditor asks for evidence that employees understood a specific policy, the timestamped acknowledgment is already mapped.
Aurora Command does not guarantee compliance outcomes. It helps you organize and document the work.
Stop Rebuilding The Governance Trail Before Every Audit
Share your framework requirements, control library, or review calendar. We will show how policies, approvals, and ownership stay current and ready to hand off, from the first draft forward.
Share your control spreadsheet or policy pack. We will show how Aurora turns governance work into reusable reviewer evidence.