Telemetry-grade evidence collection for air-gapped and regulated perimeters
Deploy Collectors Inside the Boundary. Produce Chain-of-Custody Evidence That Withstands Scrutiny.
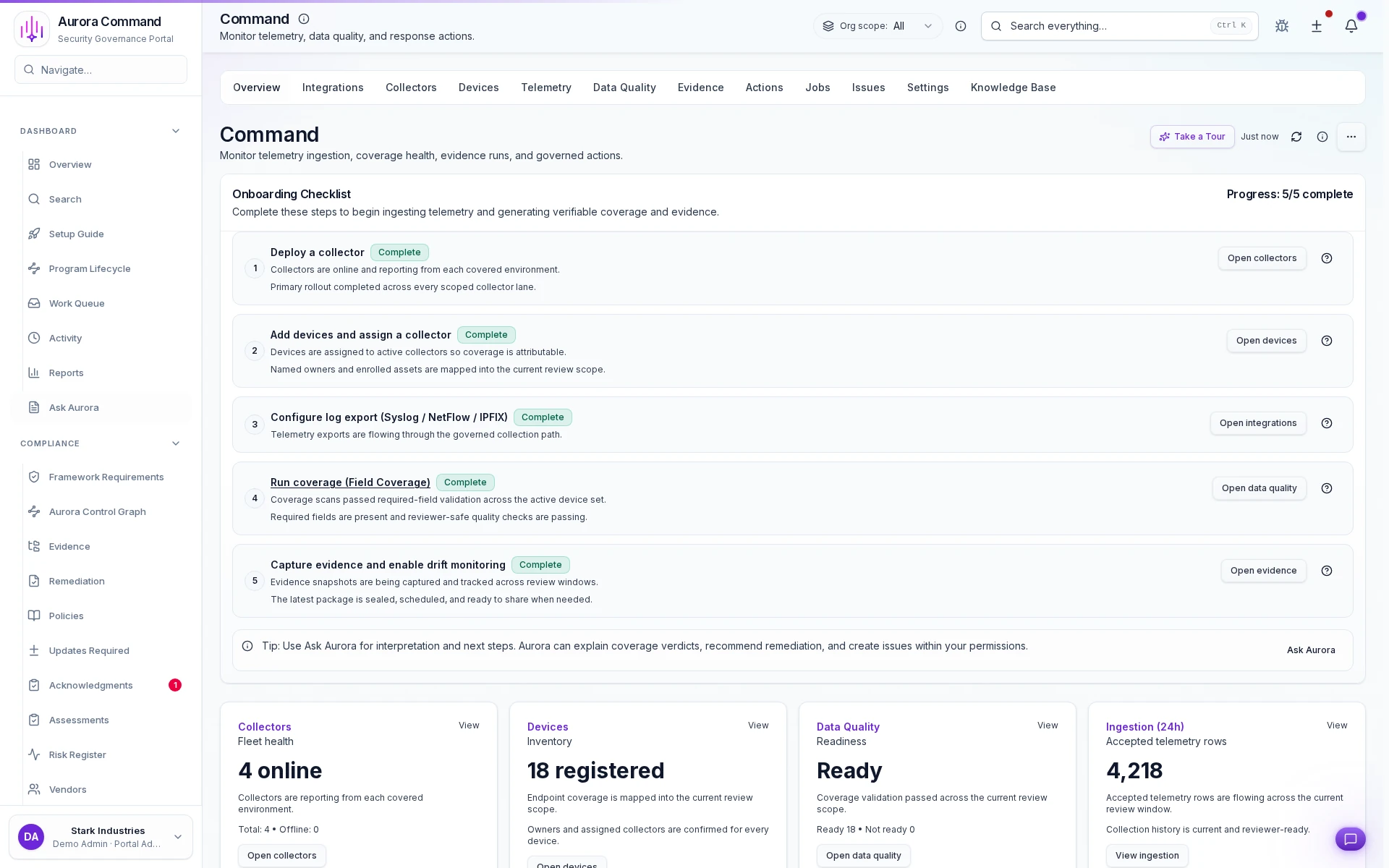
Command operations dashboard
Command Operations Dashboard
Field-Coverage Verdict With Hash Collector Health & Drift-Detection Log Governed Export With Provenance Chain
Scope the Perimeter. Deploy Collectors. Verify Every Field. Govern Every Export.
01
Define the Regulated Perimeter and Asset Scope
Aurora maps the environment boundary, enumerates collector lanes and target asset classes, and locks the proof perimeter before a single collector binary is deployed. Scope changes require explicit re-scoping approval.
02
Deploy and Attest In-Perimeter Collectors
Collectors are deployed inside the boundary with cryptographic attestation, rollout-status telemetry, and ownership records. Health heartbeats stream to the Command dashboard - no collector goes dark without an alert. Supports Palo Alto, Fortinet, Check Point, Cisco, Juniper, and 7 additional network vendors across SSH, HTTPS, and NETCONF.
03
Validate Field Coverage and Detect Drift
Field-level coverage verdicts confirm every required attribute is captured. Continuous drift detection flags configuration changes between snapshot windows so stale evidence never masquerades as current proof.
04
Layer Governed Actions via Command Control
When operational control is required, Command Control adds plan-apply-rollback execution, multi-party approval gates, and tamper-evident action logs - isolated from evidence collection so each layer carries its own audit trail.
05
Package Chain-of-Custody Exports
Aurora assembles governed export packages with integrity hashes, provenance metadata, snapshot lineage, and review-window context - ready for procurement, auditors, and external reviewers without exposing internal operational posture.
Why Air-Gapped, Hybrid, and On-Prem Environments Break the Standard Proof Model
Screenshots and Loose Exports Fail the Evidence Bar
Aurora Command deploys scoped collectors inside the perimeter so auditors and procurement receive telemetry-backed evidence with integrity hashes - not browser screenshots or manually curated spreadsheets.
Coverage Must Be Verified at the Field Level
Aurora validates every required attribute against the scoped boundary and flags drift, gaps, and stale captures - so reviewers see machine-verified coverage verdicts, not self-reported assertions.
Operational Control Requires Its Own Audit Trail
Aurora isolates governed plan-apply-rollback execution in Command Control with multi-party approvals and tamper-evident logs - so procurement evaluates the operational-control burden separately from evidence collection.
Chain-Of-Custody Artifacts That Justify the Command Deployment
The Modules That Compose Command Enterprise
01Command Insight
Scoped collector deployment, encrypted snapshot capture, field-coverage verification, and drift-detection telemetry - the foundational evidence-collection engine for regulated perimeters.
02Command Control
Plan-apply-rollback execution with multi-party approval gates and tamper-evident action logs - the governed operational layer for environments that require auditable change control.
03Command Expansion Pack
A named unit that adds environment boundaries, collector lanes, or device-scope increments with published pricing - scaling without contract renegotiation or surprise overages.
04Deployment Engineering & Premium Support
Dedicated deployment engineering, collector integration assistance, and a contractual premium-support SLA - infrastructure-adjacent work priced visibly, never buried in opaque ARR.
Where Teams Deploy Command
Defense, Intelligence, and Classified ProgramsAurora supports programs operating under CMMC, NIST 800-171, ITAR, or agency-specific ATOs where evidence must be collected inside a controlled perimeter with cryptographic provenance.Hybrid Cloud, On-Prem, and Air-Gapped EstatesDeploy Command when boundary-aware collector telemetry, governed snapshot capture, and drift detection replace the cloud-only evidence assumptions that hybrid and air-gapped estates cannot satisfy.Procurement-Heavy Security and Audit ReviewsAurora provides procurement and security reviewers with explicit Command scope, deployment-engineering costs, and premium-support terms before legal review creates deal friction.
Direct Answers About Command Deployment and Pricing
Why is Command quote-led instead of self-serve?
Why is Command quote-led instead of self-serve?
Collector deployment inside a regulated perimeter, environment-boundary scoping, drift-detection configuration, and premium-support SLAs materially change the engineering and support burden. Aurora prices that path explicitly rather than hiding infrastructure-adjacent costs inside a self-serve tier.
Why are Command Insight and Command Control separate modules?
Why are Command Insight and Command Control separate modules?
Many teams need only in-perimeter evidence collection - collectors, snapshots, field-coverage verification, and governed exports. Others also require plan-apply-rollback execution with multi-party approvals. Separating the modules lets procurement evaluate and fund each capability independently.
Does Command replace the rest of the Aurora platform?
Does Command replace the rest of the Aurora platform?
No. Command extends the platform into environments where in-perimeter collector deployment, drift detection, and chain-of-custody exports are required. The core Aurora platform continues to handle the broader governance, readiness, and reviewer-operations story.
Can procurement review Command terms before a full deployment pilot?
Can procurement review Command terms before a full deployment pilot?
Yes. Aurora publishes the deployment-engineering package, premium-support minimums, expansion-unit economics, and Command scope model early so procurement and legal can evaluate the commercial path before committing to a pilot.
Describe the Perimeter. We Will Scope the Collectors, the Coverage, and the Export Governance.
Share the environment boundary, the compliance framework, and the evidence bar your reviewers require. We map the collector deployment, field-coverage verification, drift-detection posture, and governed-export packaging - then determine whether Command Insight, Command Control, or the full Command Enterprise plan fits.
Tell us the perimeter, the framework, and the evidence bar. We scope collectors, coverage, and export governance - then show you the Command deployment that fits.