Feature
IP Allowlisting: Keep reviewer and operator access inside approved network ranges.
IP allowlisting is part of Aurora's named enterprise-controls surface. Define allowed CIDRs, enforce warn or block modes, and use time-bound break-glass paths when you need to recover access safely.
Keep reviewer and operator access inside approved network ranges.
- Approvals stay attributable:Policy, control, and decision changes keep a visible owner and review trail.
- Controls map once:Reuse the same operating record across overlapping frameworks and reviewer asks.
- Evidence stays tied in:Governance decisions stay connected to the proof and timestamps behind them.
- Changes stay defensible:Keep the program current between audits instead of rebuilding the story from scratch.
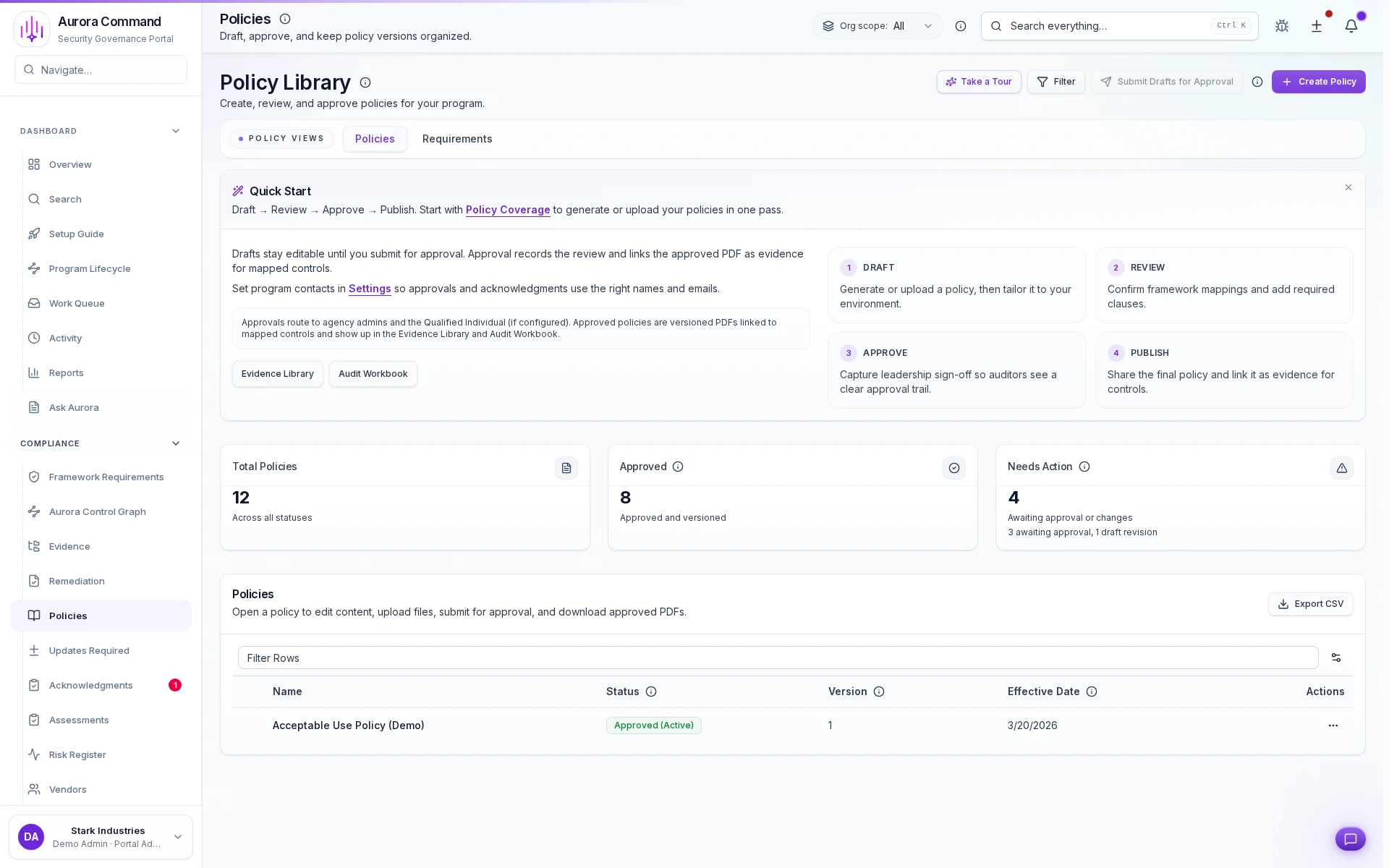
Sample output
Security policy configuration record
Versions and approvals
Policy And Approval Workspace
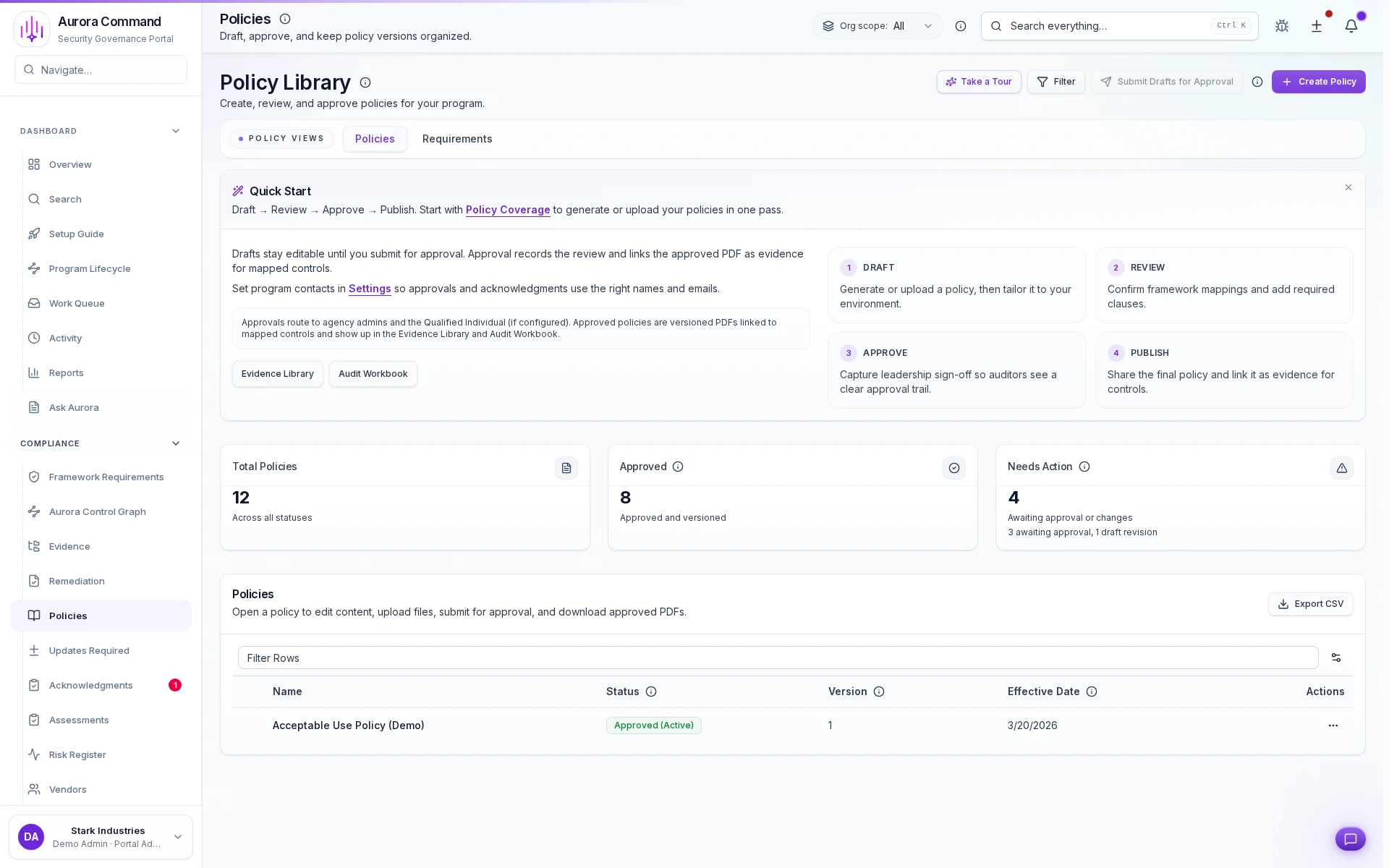
How Teams Keep Policies Approved And Current
01
Start from the current policy set
Centralize the policy library so teams stop managing versions across folders and email threads.
02
Route changes to the right owners
Keep legal, security, and executive reviewers attached to the same approval path.
03
Approve and publish new versions
Preserve version history and sign-off records instead of relying on informal acknowledgments.
04
Map policies to frameworks
Reuse the same operating record across overlapping frameworks and buyer asks.
05
Export the current record on demand
Share the live version, approval history, and supporting context without scrambling for files.
What This Adds To Policy Operations
Designed for
Enterprise procurement • SOC 2 • Buyer security reviews
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Connect Policy Work To The Rest Of The Program
Questions Teams Ask
How do policies, controls, and approvals stay tied together?
How do policies, controls, and approvals stay tied together?
Aurora keeps version history, ownership, approvals, and related evidence attached so the governance record is easier to defend later.
What does the team actually share from this work?
What does the team actually share from this work?
Teams usually share Security policy configuration record; Break-glass activation log; Access enforcement audit events. The goal is to give reviewers the right package without making them reconstruct how the program operates.
Where does this help most in recurring audits?
Where does this help most in recurring audits?
It fits best when the team is handling Enterprise procurement, SOC 2, Buyer security reviews and needs the work to stay reusable instead of being rebuilt each cycle.
What changes after rollout?
What changes after rollout?
Enforce network boundaries for portal access Reduce exposure to credential compromise
Share The Framework, Control Set, Or Policy Review You Keep Rebuilding.
We’ll show how Aurora keeps approvals, change history, and evidence connected so the next review starts from current work.
Share one request and we will show the path to security policy configuration record without losing approvals, ownership, or reviewer context.