Feature
Encrypted Evidence Snapshots: Store config evidence with integrity you can prove.
Capture encrypted snapshots with hashes and drift detection so you can prove what configuration existed at a point-in-time, without relying on screenshots.
Store config evidence with integrity you can prove.
- Collector rollout is visible:See which nodes are live, blocked, or missing before review day arrives.
- Coverage proof is exportable:Turn device status, readiness gates, and snapshots into reviewer-safe artifacts.
- Signals stay grounded:Pull in telemetry and infrastructure context without exposing raw systems to buyers.
- Evidence keeps integrity:Snapshots and operational history preserve what changed, when, and why it matters.
Sample output
Snapshot object with hash chain
Verifiable proof reviewers can follow
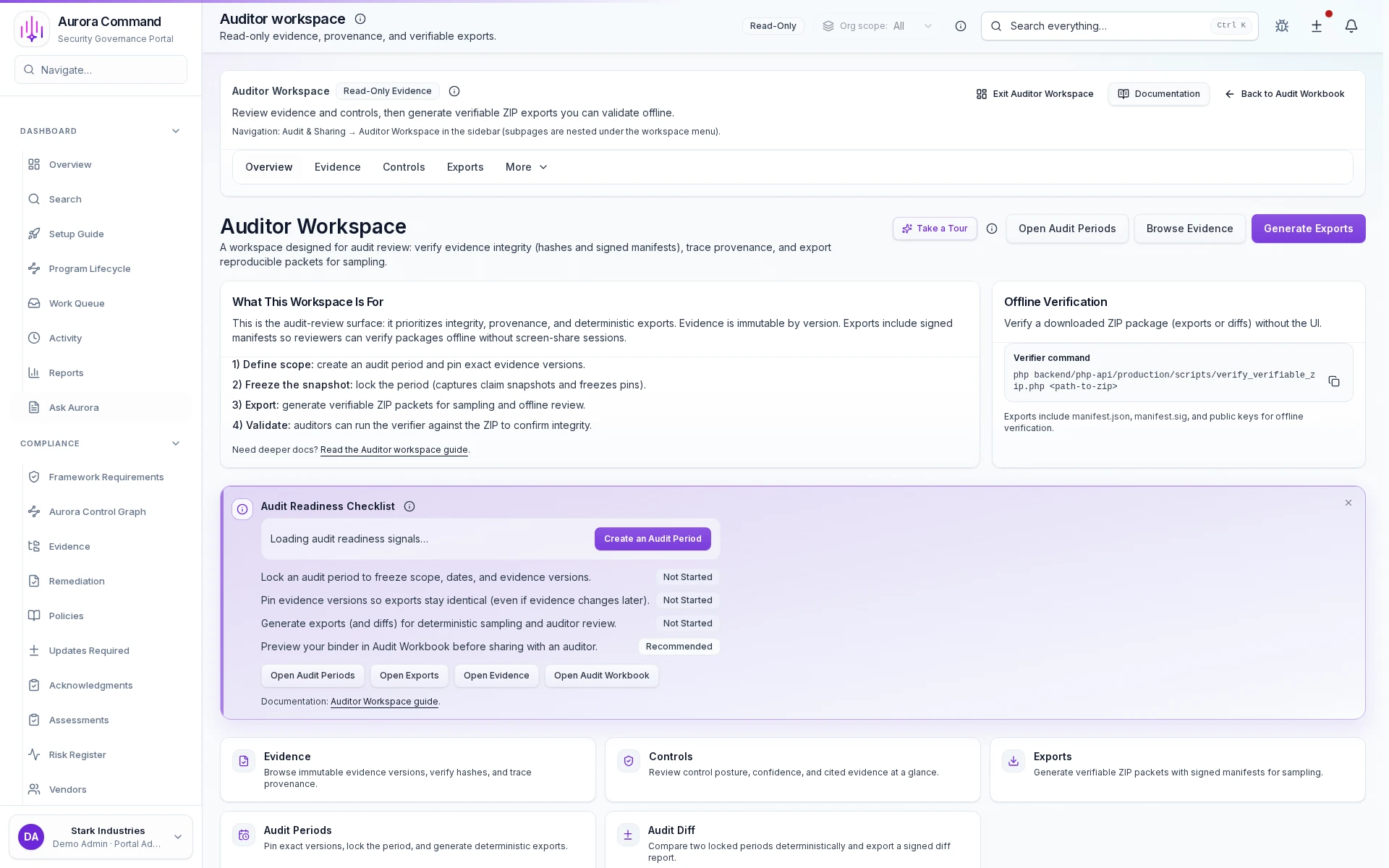
Auditor Workspace
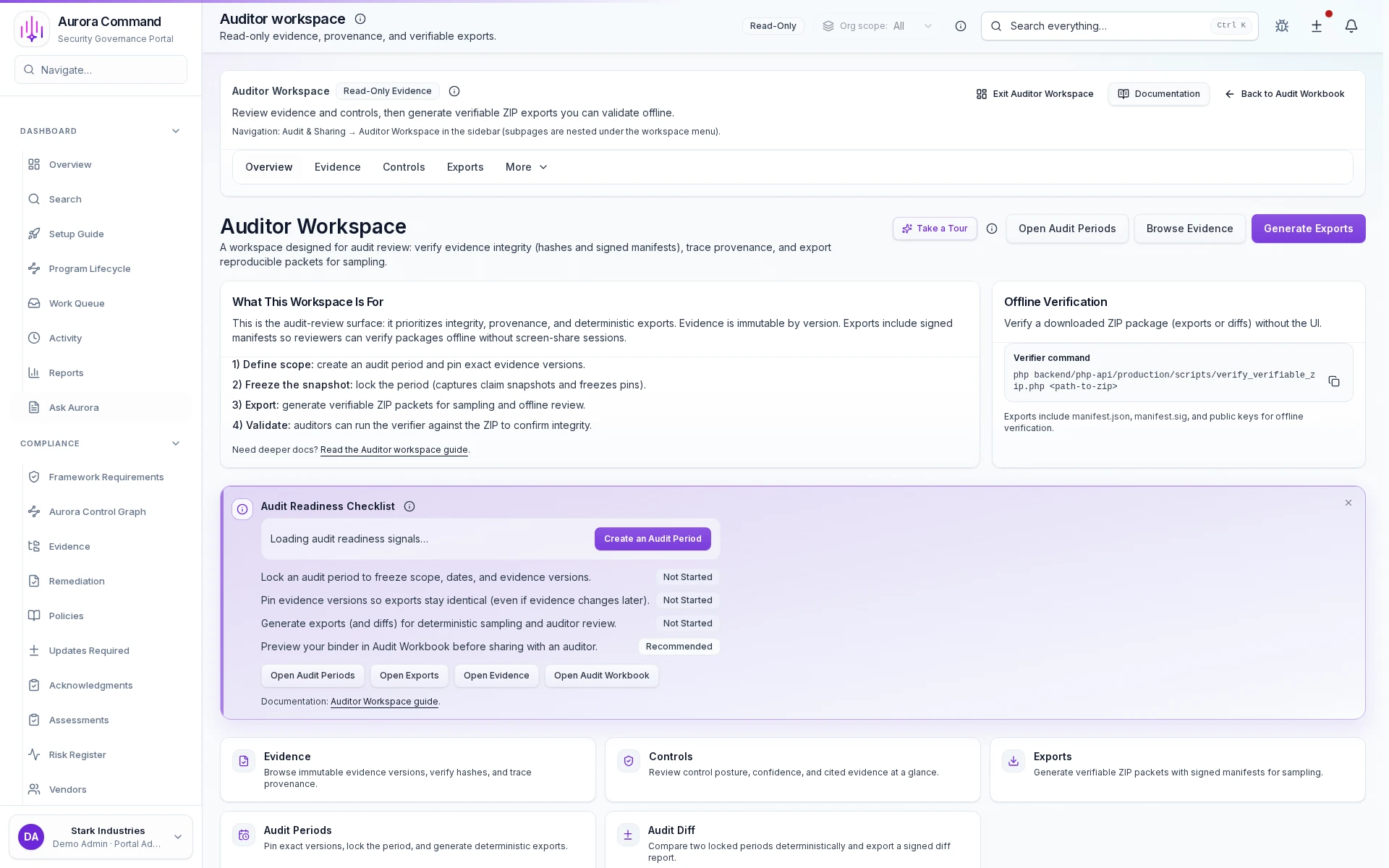
How Teams Package A Review Window
01
Define the review window
Set the time period and scope so everyone is looking at the same operating record.
02
Freeze the right evidence set
Preserve what was true for that review window instead of letting later changes blur the record.
03
Generate reviewer exports
Package the materials reviewers expect without exposing the full internal workspace.
04
Track period-over-period change
Show what changed and why it matters without making reviewers compare folders manually.
05
Hand over a defensible package
Give auditors and buyers a clear proof trail they can navigate quickly.
What This Adds To Audit Handoff
Designed for
CMMC • SOC 2
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Connect The Systems Behind Each Review Period
Questions Teams Ask
What does this prove that SaaS-only capture cannot?
What does this prove that SaaS-only capture cannot?
Command is built for environments where buyers or auditors need proof from infrastructure you cannot expose directly. It keeps rollout, coverage, and integrity signals on the record.
How do collectors and readiness gates show up for reviewers?
How do collectors and readiness gates show up for reviewers?
Teams usually share Snapshot object with hash chain; Drift history export. The package is designed to show rollout status, coverage, and data-quality proof without making a reviewer interpret raw telemetry.
Can we export coverage without exposing raw systems?
Can we export coverage without exposing raw systems?
Yes. Aurora turns the underlying signals into reviewer-safe artifacts so you can prove coverage without handing over direct infrastructure access.
What changes after rollout?
What changes after rollout?
Preserve defensible evidence Detect drift over time
Tell Us About The Environment That Cannot Leave Your Network.
We’ll show how Command turns rollout status, coverage, and integrity signals into reviewer-safe proof.
Share one request and we will show the path to snapshot object with hash chain without losing approvals, ownership, or reviewer context.