Feature
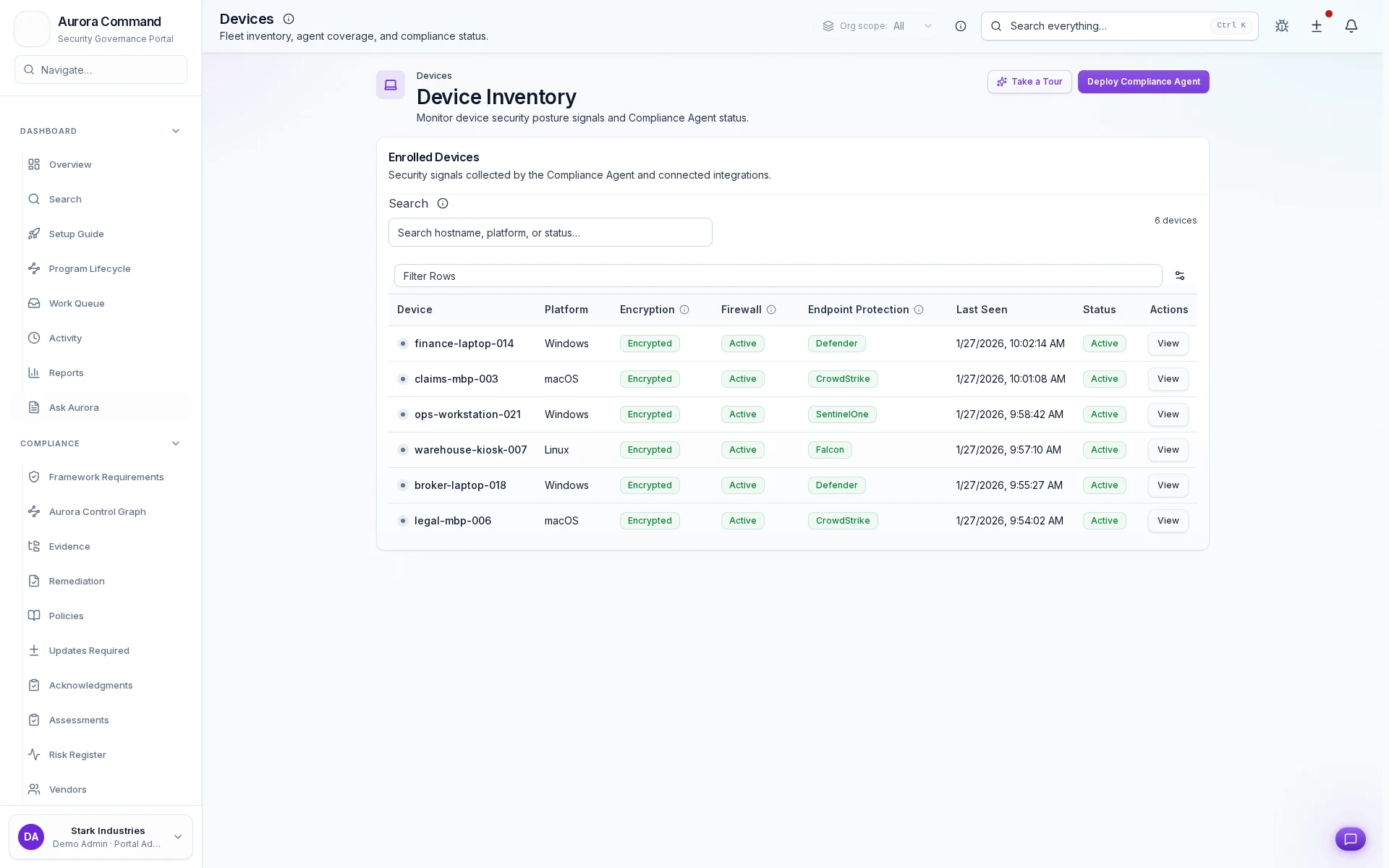
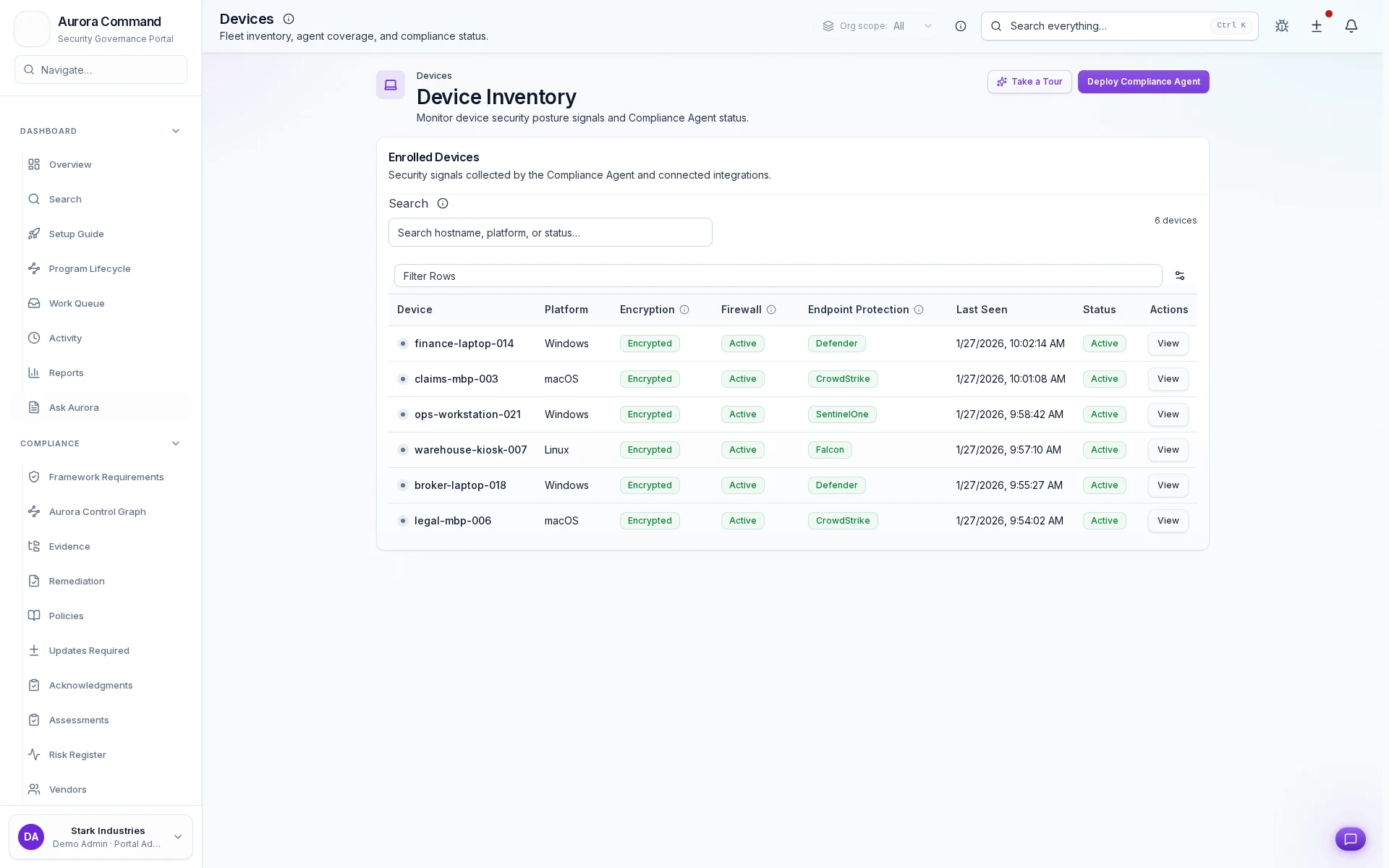
Endpoint Security Evidence: Prove endpoint coverage, encryption, and firewall status.
Aurora tracks device inventory and endpoint security status evidence. Answer buyer questions about encryption, management coverage, and host firewall standards with exports, not anecdotes.
Prove endpoint coverage, encryption, and firewall status.
- Freshness is visible:Timestamps, source history, and owner context stay attached to every record.
- Connectors keep pace:Automated capture reduces screenshot chasing and spreadsheet rebuilds.
- Exports stay review-ready:Package evidence into reviewer-safe bundles without losing traceability.
- Reuse across frameworks:Map the same evidence into overlapping control sets instead of recollecting it.
Sample output
Device security status report
Governed report
Device Coverage Workspace
How Teams Prove Endpoint Coverage
01
Connect endpoint and identity sources
Connect device inventory and ownership into Aurora from the systems teams already rely on.
02
Normalize inventory and coverage
Create a single operating view of what is managed, missing, or outside policy.
03
Check posture and protection status
Track encryption, firewall, management, and related controls in a way reviewers can understand.
04
Route coverage gaps to owners
Turn missing coverage into accountable follow-up instead of a last-minute audit scramble.
05
Export coverage proof for review
Share reviewer-safe status reports that replace manual screenshots and spreadsheets.
What This Adds To Endpoint Reviews
Designed for
SOC 2 • CMMC
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Connect The Endpoint Tools Security Teams Ask About
Questions Teams Ask
How does Aurora prove the evidence is current?
How does Aurora prove the evidence is current?
Every record keeps source, timestamps, ownership, and review history visible so stale proof is easier to catch before a buyer or auditor does.
Can the same evidence support multiple frameworks?
Can the same evidence support multiple frameworks?
Yes. Aurora is built so one evidence record can support overlapping control mappings instead of being recollected for each framework.
What can we share without exposing internal systems?
What can we share without exposing internal systems?
Teams usually share Device security status report; Coverage attestations. The exported package keeps the proof trail intact without opening direct access to the underlying systems.
What changes after rollout?
What changes after rollout?
Demonstrate endpoint program maturity Reduce audit effort for device controls
Share The Evidence Request That Keeps Slowing The Team Down.
We’ll show how Aurora keeps source history, freshness, and reviewer-safe exports tied to the same record.
Share one request and we will show the path to device security status report without losing approvals, ownership, or reviewer context.