Product Module
Stop Rebuilding Vendor Reviews Every Cycle.
Run vendor due diligence with structured intake, tiered assessments, decision trails, and recurring review cadence that carries forward instead of resetting.
Share your vendor list or a recent review. We will show how it becomes a repeatable, auditable workflow in 15 minutes.
Best fit
Vendor RiskExpand to Risk & Accountability when the workflow broadens.
Best for vendor inventory, due diligence, and repeatable follow-ups with evidence attached.
The Difference Between Chasing Vendors And Managing Them
Without Aurora
- Vendor inventory lives in a spreadsheet that's outdated the day after it's built
- Due diligence means sending a questionnaire via email and chasing responses for months
- Re-assessment cycles are missed because nobody tracks when vendor reviews are due
- No connection between vendor risk findings and the remediation work they generate
- Auditor asks for your vendor risk posture and the team builds a summary from scattered emails
With Aurora
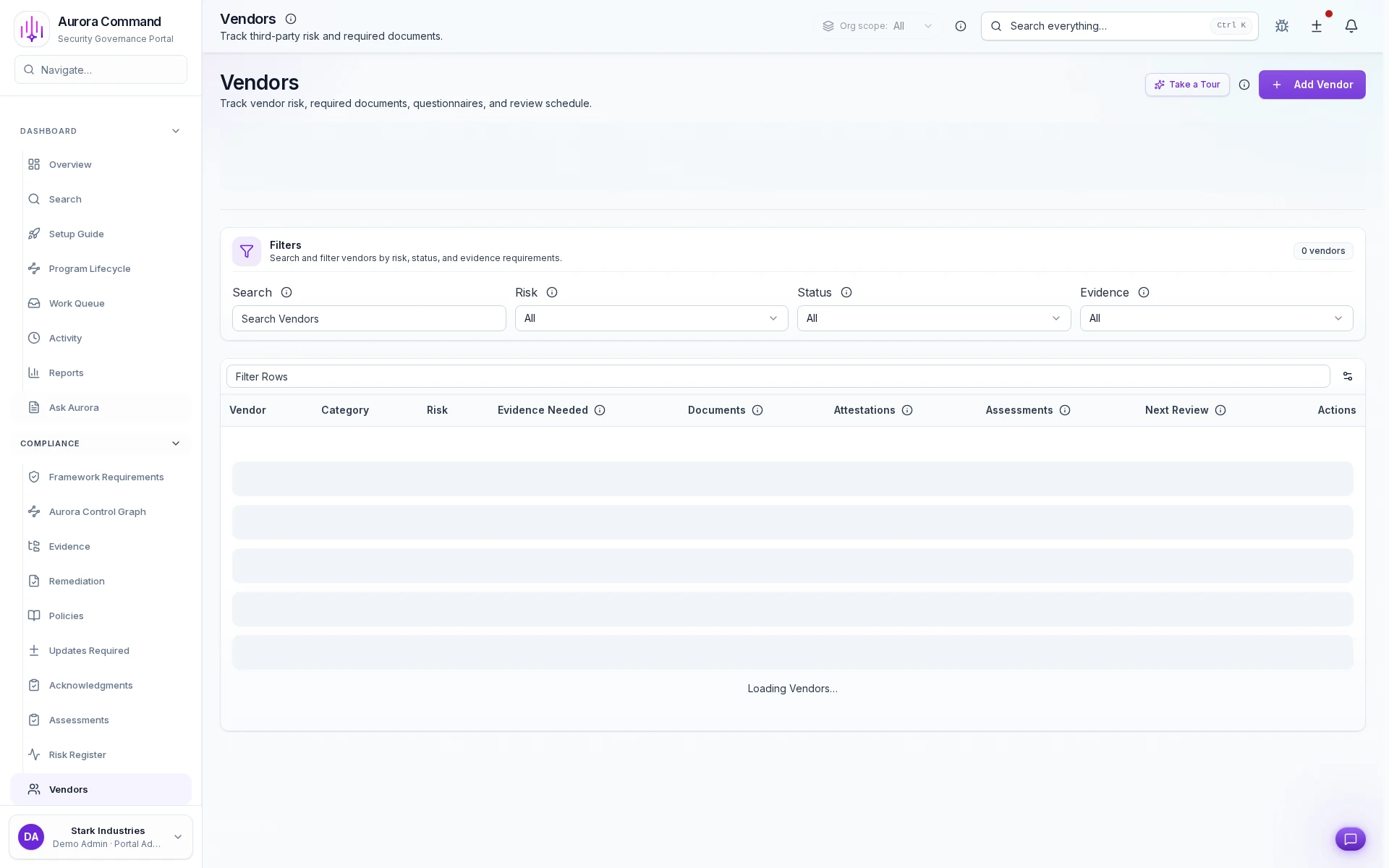
- Living vendor registry with tiered classification, review status, and due diligence state per vendor
- Structured due diligence workflows with automatic reminders, response tracking, and evidence collection
- Automated re-assessment scheduling with cadence tracking and escalation when reviews go overdue
- Every vendor finding converts to an owned remediation task with deadline, evidence, and closure tracking
- Vendor risk posture exportable on demand with tiering, due diligence status, and follow-up history
Vendor Risk
Best for vendor inventory, due diligence, and repeatable follow-ups with evidence attached.
- Risk & Accountability: Add accountable remediation and closure trails around third-party findings.
- Reviewer Operations: Add cleaner sharing and request routing when buyers or auditors need to see the third-party story too.
Need help choosing?
Compare bundles and module pricing to find the right starting point, then confirm fit in a walkthrough if your workflow is regulated or time-bound.
From First Vendor Intake To Recurring Due Diligence
01
Capture scope, data access, and risk tier on intake
Record data classification, business criticality, regulatory exposure, and contractual obligations in one structured intake. Risk tier determines assessment depth, reassessment cadence, and escalation thresholds from the start.
02
Run tiered assessments with owner and deadline accountability
Send risk-appropriate questionnaires, collect vendor-submitted artifacts and certifications, and track who owes what by when. Critical vendors get deeper scrutiny automatically; low-risk relationships get lightweight intake.
03
Document every decision with approver rationale
Record the approver identity, written rationale, timestamp, and acceptance window behind every approve, flag, reject, and exception. Auditors trace any vendor decision back to its source without chasing email threads.
04
Enforce reassessment cadence by risk tier
Schedule quarterly, semi-annual, or annual reviews so vendor posture stays current between audits. Each reassessment builds on prior evidence with change tracking, so assessors see what changed instead of starting from scratch.
05
Give every stakeholder the view they need
Procurement sees contract and compliance status. Legal sees decision trails and exceptions. Security sees risk scores and certification gaps. One vendor record, role-scoped access, shared evidence history.
The Numbers Behind Structured Vendor Programs
0x
Review Cycle Efficiency
Structured workflows with reusable questionnaires and automatic follow-up cut vendor review turnaround by two-thirds.
0%
Re-Assessment Coverage
Automated scheduling ensures every vendor is reviewed on cadence - no more missed cycles or stale assessments.
< 0 hr
Finding Response Time
Vendor risk findings route to owned tasks with deadline tracking, cutting response lag from weeks to days.
Key Capabilities
Feature 1 of 6: Structured Intake with Risk Context from Day One
1/6
Structured Intake with Risk Context from Day One
Every vendor starts with the same risk context: data classification, business criticality, regulatory exposure, and contractual obligations. Intake decisions stay comparable and auditable across hundreds of relationships.
Artifacts reviewers recognize, plus sample previews of structure.
Scroll for artifact previews
Sync Vendor Assessments With Your Work Tools
Extend This Workflow
- RiskRisk register, remediation ownership, and closure evidence across programs.
- AssessmentsStructured assessments with tiered depth, evidence collection, and reviewer attribution.
- EvidenceCentralized evidence repository with version tracking and audit-ready exports.
- Support RequestsVendor-facing intake with SLA tracking, task routing, and closure evidence.
- Trust CenterPublic-facing compliance posture with self-service evidence access for prospects and partners.
- Support Requests DemoSee how vendor-facing support requests flow from intake to closure with evidence.
- Trust Center DemoWatch the Trust Center in action with self-service evidence sharing and NDA gating.
Common Questions About Vendor Risk Management
Can we standardize questionnaires across vendor types?
Can we standardize questionnaires across vendor types?
Yes. Create questionnaire templates by vendor tier or category. Reuse approved questions while customizing for specific vendor types where needed. When a new vendor enters intake, the system auto-selects the right template based on risk tier and data access classification so assessors start from a consistent baseline.
How does reassessment cadence work?
How does reassessment cadence work?
Set review frequency by risk tier: quarterly for critical vendors, semi-annually for moderate risk, annually for standard relationships. Each reassessment starts from the prior cycle's evidence with change tracking, so assessors see what changed instead of starting from scratch. Overdue reassessments surface on dashboards and trigger escalation notifications automatically.
Can procurement and legal teams see vendor risk status?
Can procurement and legal teams see vendor risk status?
Yes. Role-scoped views give procurement, legal, and security teams structured access to vendor profiles, due diligence status, and decision history without full platform access. Each stakeholder sees the fields and decisions relevant to their function so cross-team coordination happens on one record instead of forwarded spreadsheets.
How do vendor risk records connect to our compliance program?
How do vendor risk records connect to our compliance program?
Vendor profiles link to the controls they affect across every mapped framework. When a SOC 2, ISO 27001, or custom framework requires vendor risk management evidence, the assessment records, decision trails, and reassessment history are already linked and exportable. No manual cross-referencing or last-minute assembly.
What happens when a vendor fails an assessment or a certification lapses?
What happens when a vendor fails an assessment or a certification lapses?
Failed assessments and lapsed certifications trigger automatic alerts to the vendor owner and escalation contacts. The system records the event with a timestamp, requires a documented response (remediation plan, exception request, or termination recommendation), and tracks the resolution to closure with attached evidence. Nothing resolves silently.
Can we import our existing vendor inventory?
Can we import our existing vendor inventory?
Yes. Import vendor records from spreadsheets, prior assessments, or procurement systems. Each imported vendor enters with risk context fields pre-populated where available and gets immediately enrolled in the tier-appropriate reassessment cadence. Existing evidence and questionnaire history attach to the new vendor record so prior work is not lost.
End The Cycle Of Rebuilding Vendor Reviews From Scratch
Share your vendor list and we will show a repeatable, auditable due-diligence workflow in 15 minutes.
Share one vendor review packet. We will show how Aurora keeps questionnaires, evidence, and follow-ups tied to the same record.